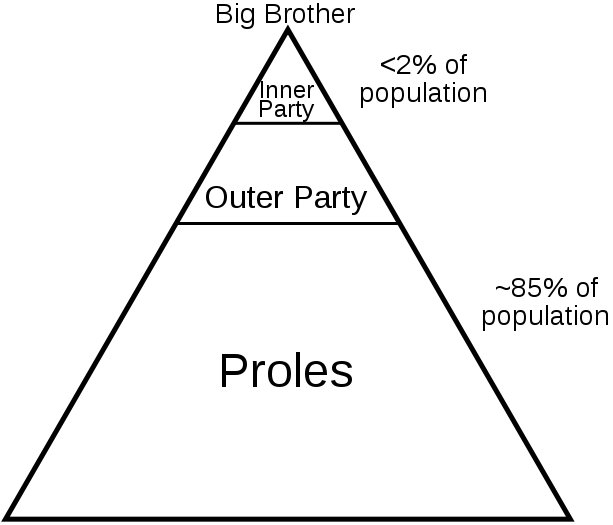
The social and political classes in George Orwell’s novel 1984
We’ve all been told that there is no such thing as privacy on the Web. That is true. Still, we are not helpless. Recently I got quite angry after I learned about a whole new category of privacy threat on the Internet — shady private organizations that collect data on you and then give it, or sell it, to the government. Glenn Greenwald posted an article on this a couple of weeks ago.
This motivated me to put a little time and research into figuring out how to attain a reasonable level of privacy on the Web with a reasonable effort. I was not interested in what I’d call a paranoid level of privacy. That would take a great deal of effort and would make it much harder, and less fun, to use the Internet. But surely, I thought, there is a reasonable level of defense that anyone could achieve with a little study and some changes in how you set things up on your computer.
There are three broad categories of privacy and security risk on the Internet:
1. Illegal activity. This would include password “phishing” scams, spyware, viruses that take over your computer and turn it into a “bot” under the control of spammers, etc.
2. Activity that is legal but extremely intrusive. This includes efforts to track you and identify you on the Internet, the better to target ads to you or to sell you something. This is extremely common, and it’s getting worse.
3. Tracking aimed at the ability to build dossiers on millions of Americans, names and all, that can be sold to the government or otherwise used against you. It was this type of activity that Greenwald (Greenwald is a Constitutional lawyer) was writing about in the link I posted above.
For category 1, your best defense is to keep your computer up to date with security fixes of the type that are regularly released by Microsoft and Apple.
For categories 2 and 3, there is much you can do to defend yourself by making some changes in how your configure your computer.
I’m going to list some steps that I took — and that you can take — with a brief description of the privacy threat and how the threat can be reduced. Please appreciate that I can’t answer questions about how to make these changes on your computer. Instead, you should do your own research and learn about how to manage these things. Then you’re on your way to empowering your own self defense.
1. Use two browsers. One of the ways that snoops can figure out your identity is to snitch your identity from sites that you sign into. I am particularly wary of Yahoo, Facebook, and Google. If you are signed into them, they know who you are. Clever tracking cookies can then identity you by name on other sites. For example, recently the Washington Post’s web page started displaying a new feature that shows (among other things) what you and your friends on Facebook have been reading on the Washington Post web site. The Washington Post was quick to put out a disclaimer about why this is no threat to your privacy. You decide. As far as I’m concerned, it’s yet another reason to ignore the Washington Post, which (to my judgment) is no longer a real newspaper but merely a mouthpiece for the Washington establishment.
So here’s what I did. I use a Macintosh, and my regular browser is Safari. I downloaded Google Chrome to use as a second browser. One browser is my “identity” browser, and the other is my “no-identity” browser. When I sign in to Facebook, I do that in the “identity” browser, Google Chrome. But I don’t go anywhere else in that browser. Someone could glean my identity from Facebook and track me all day, but they’d only discover that I didn’t go anywhere but Facebook.
I do the rest of my browsing in Safari. But when browsing in Safari, I never sign in anywhere. The other important step is to delete all your cookies. Now, cookies may do a couple of things for you that you like, like enable a web site to remember that you’ve been there before. But it’s actually pretty easy to browse happily without those minor conveniences that cookies can give. Mostly, cookies are there to support the business models of the web sites you visit, whether legitimate or snoopy. But I don’t care about anyone’s business model on the web. I care much more about my privacy. Delete your cookies frequently, even once a day. If you haven’t looked at your cookies in a while, you may be stunned to find that you have thousands of them. Cookies are being used more and more, and mostly they are being used against you.
2. Use a DNS other than your internet service provider’s DNS. I cannot explain here what DNS is or tell you how to change your computer’s DNS settings. You must do your own research and understand it well enough to make this change for yourself. My ISP is Verizon. But that doesn’t mean I have to use Verizon’s DNS. I use Google’s free, public DNS. Though I am increasingly suspicious of Google’s commitment to privacy, their written privacy policy for their public DNS does explicitly say that they won’t match your DNS lookups with other data that Google may have about you. They also say that they destroy their DNS logs on a regular basis. Based on what I know at this time, I’d rather have my DNS data logged at Google rather than Verizon. And besides, Google’s DNS service is better than Verizon’s. Here is a link to information on Google’s public DNS.
3. Get Adobe Flash under control. I’ve mentioned previously how Adobe Flash has become one of the most obnoxious players on the web. It’s for good reason that Apple’s Steve Jobs is doing battle with Adobe over Flash. Flash eats your bandwidth with unwanted fancy ads. It eats up your computer’s processing power, and, if you’re on a laptop or a handheld, will run down your battery quickly. Even worse, Adobe Flash operates totally outside of your browser’s security features. Flash’s default security settings are wide open. By default, Flash can set its own “Flash cookies,” which are much harder to find and delete because your browser doesn’t know about them. Flash permits web sites to store data on your computer. Flash even may permit some web sites to use your internet bandwidth for “peer assisted networks.” My guess is that, 10 years ago, Flash already had everything that is of interest to you as a web user. Their development effort, clearly, is focused on giving advertisers and the operators of web sites the tools they want to track users, gather data on users, and focus advertising on users. I don’t care about any company’s revenue. I care more about my privacy. So I took these steps:
a. Get a Flash blocker plug-in. For Safari, I use ClickToFlash. There are different Flash blockers for other browsers. Do some Googling for “flash blocker” plus the name of your browser, and you’ll find a way to keep Flash from running in your browser unless you explicitly give it permission.
b. Delete your Flash cookies. You may have hundreds or thousands of them. On the Macintosh, you can find them in the file system at ~/Library/Preferences/Macromedia/Flash Player/#SharedObjects. Drag them all to the trash. They are not benefiting you in any way. They are only benefiting someone’s revenue model. If you use a computer other than a Mac, Google for “flash cookies” or “flash shared objects” and see if you can’t find some instructions. Remember, I can’t help you with this. I’m only suggesting that it’s something you might want to research for yourself.
c. Change the default settings of Flash on your computer. To do this, you must go to Adobe’s web site. Lock it up as tight as possible. None of those features benefit you in any way. They all benefit those who want to track you or make money off you. I believe that Adobe intentionally makes it difficult to change the privacy and security settings in Flash. Adobe is one of the meanest players on the web today. They do not deserve our support.
4. Use a proxy service. Using a proxy service full time, at least in my judgment based on what we know at this time, is probably more trouble than it’s worth. Still, if I wanted to do something on the web that might be considered suspicious or that I think might attract attention (for example, visiting the WikiLeaks web site), then I would use a proxy service temporarily. Again, you must do your own research, but proxify.com is a good place to start.
Good luck and happy browsing. And please remember, I can’t answer questions or help you make these changes on your computer. I’d rather see you empowered to handle your own self-defense on the Internet. It’s a jungle.