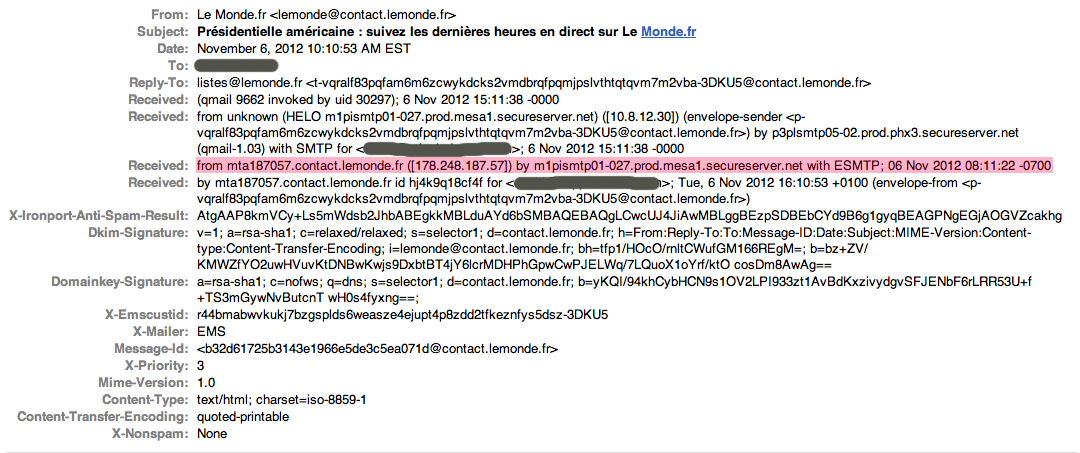
The media today are focusing on the downfall of David Petraeus, the former CIA director. The Atlantic has a piece on how the FBI snooped on Petraeus and his mistress. It was from identifying information in the header of Google email.
All email has a header. Most email programs show only the “To:”, “From:”, and “Subject:” fields, etc. But there are other fields that give information about the computers that sent and received the email as it made its way across the Internet. In the example above, I have grayed out the parts that identify me and put a red stripe over the part that identifies the sender. (Click on the image for an enlarged, more readable version.) The email above was sent by a computer with the IP address 178.248.187.57. A “traceroute” command (any nerd knows how to do a traceroute command) shows that that IP address is in Paris.
By default, all email servers include this information, as far as I know. The only way to avoid it is to stay away from corporate email and free email services such as Google or Yahoo. There are paid email services that are more secure. For example, Neomailbox.com offers an email service that suppresses this information. Their servers also are offshore, in Switzerland. That will cost you about $50 a year.
It blows my mind that a CIA director would be so stupid as to allow career-destroying email to touch Google’s gmail servers. Not only does gmail include identifying information in the headers, Google also will happily turn your email over to any goon who asks for it — local, state, or national. And when you sign up for Google’s gmail you give Google permission to read it all — incoming and outgoing — to build a dossier on you.
You get what you pay for. Use gmail and Yahoo at your own risk.
Here are some guidelines for secure use of email:
1. Don’t use free email services such as Google or Yahoo.
2. Never use your work email for anything that would embarrass you or anyone else.
3. Don’t allow your email to be archived on someone else’s server. If you use IMAP, your email is being archived. POP3 is more secure, because the mail can be deleted off the server a day or two after it is downloaded to your computer.
4. Consider a secure, offshore email service such as Neomailbox.com.
5. Consider encrypting your email with an email client such as Thunderbird, which supports a PGP encryption plug-in. A PGP encryption plug-in also is available for the Macintosh mail program.
6. Never forget that when your email crosses the Internet, it’s like a postcard in the mail — anyone who has access to the servers and routers that handle the email can read it, because it’s clear text. A typical email may pass through a dozen or more routers on its way to its destination. It’s also commonly assumed that the U.S. government is capturing and storing a copy of virtually everything that travels over the Internet. If that’s true, encryption is the only defense. Setting up encryption is not that hard, but I’ve never been able to persuade a single person to do it.

How about not doing something as stupid as the 3 people did; have an affair, email each other, threaten one and then as Gen Allen’s case send email of some type to the other woman… and they call the little guy out of touch… I’d used the US mail to communicate, then it would self destruct after 3 minutes
These people have committed several sins. Never mind that our spies and spooks are being commanded by a man so technologically unsophisticated. Lost in all the noise these days, buried beneath the mountains of pills and blinding flurries of pharmacy scripts and endless social-media self-presenting is the stuff about which Freud and Jung were correct, the stuff about which most Americans try very hard not to think.
-That woman has daddy issues.
-That guy couldn’t get a date in high school.
-Power is exciting, and it makes very smart people do very dumb things, especially when it falls into the hands of people who have been severely repressing themselves for a long, long time.